Azure Private Link
The Secret Tunnel to Services
Simply Put...
Imagine your house is a private, secure network, and you want to get a pizza from a special pizza place (an Azure service) without ever stepping outside. Usually, the pizza delivery person has to come to your front door, which is like a public entrance. But with Azure Private Link, it's like having a secret tunnel that connects directly from your kitchen to the pizza place's kitchen! You can get your pizza through this tunnel, and no one from the outside world can see or intercept it. The end of the tunnel in your kitchen is called a 'Private Endpoint'. It's a private and secure way to access services without exposing them to the public internet. This means that all the communication between your home network and the pizza place happens through this private tunnel, making it super secure. You can even connect your friend's house (another virtual network) or your office (on-premises network) to this secret tunnel system. This way, you can all share the same secure and private access to the pizza place, without anyone having to go out on the public street. It's all about keeping your data safe and sound within a private, protected environment.
How it Works
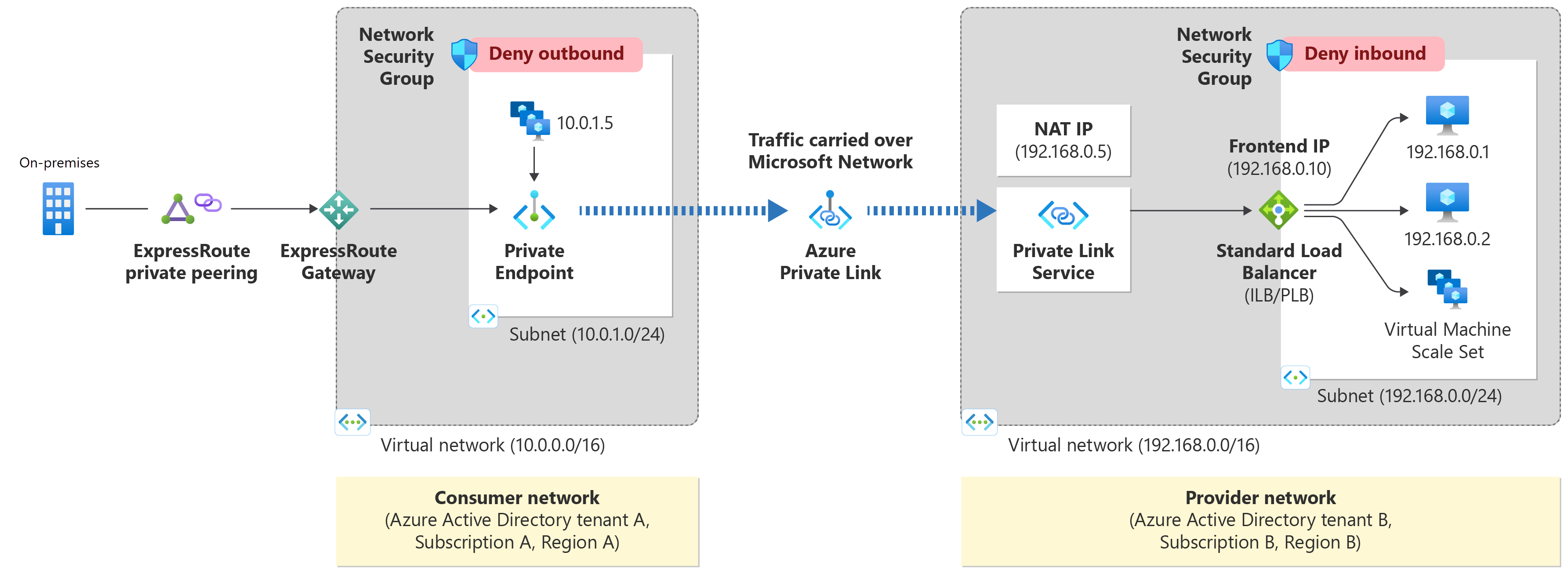
Azure Private Link works by creating a private endpoint, which is a network interface, within a consumer's virtual network (VNet). This private endpoint is then mapped to a specific instance of an Azure PaaS service, a customer-owned service, or a partner service that is running behind an Azure Standard Load Balancer. When a client in the VNet communicates with the service, the traffic is directed to the private endpoint. From there, the traffic travels securely over the Microsoft Azure backbone network to the service. This connection is a one-way street; the service provider cannot initiate connections into the consumer's VNet. This architecture effectively brings the Azure service into the consumer's private network, making it accessible via a private IP address and eliminating the need for public IP addresses, gateways, or NAT devices. For on-premises connectivity, ExpressRoute with private peering or a VPN tunnel can be used to connect the on-premises network to the Azure VNet, allowing on-premises applications to securely access Azure services through the private endpoint.
Scalability Superpowers
Azure Private Link is designed for scalability and high availability. It allows you to connect to services across different Azure regions, enabling global reach for your applications. You can create multiple private endpoints for the same service in different VNets or even in the same VNet, allowing for flexible and scalable network architectures. Since the service is built on the Azure backbone, it can handle large volumes of traffic with low latency. The NAT (Network Address Translation) capabilities of the Private Link service allow for overlapping IP address spaces between the consumer and provider networks, which simplifies network management and enhances scalability.
Key Parts
- Azure Private Endpoint: A network interface with a private IP address from your virtual network. It represents a specific Azure service in your VNet, allowing you to connect to it privately.
- Azure Private Link Service: This is what you create when you want to offer your own service to other consumers through Azure Private Link. It's the service provider side of the equation, which allows others to create private endpoints to your service.
- Azure Backbone Network: The high-speed, private network that connects all of Azure's datacenters. All traffic using Azure Private Link travels over this secure backbone, avoiding the public internet.
Security Features
- 🛡️Private Connectivity: By keeping traffic on the Microsoft backbone network, Azure Private Link eliminates exposure to the public internet, reducing the risk of cyberattacks.
- 🛡️Data Exfiltration Protection: Private Endpoints map to a specific resource instance rather than the entire service. This prevents data leakage by ensuring that consumers can only access the specific resource they are authorized to, and not other resources within the service.
- 🛡️Network Policy Enforcement: You can use Network Security Groups (NSGs) and Application Security Groups (ASGs) to control traffic to the private endpoint, allowing for granular access control.
- 🛡️Secure On-Premises Access: Securely connect your on-premises networks to Azure services using Azure ExpressRoute private peering or VPN tunnels, without traversing the internet.